Japan’s manufacturing and process industries are balancing long‑lived assets with growing expectations for data‑driven operations and cross‑site visibility. Interoperability is essential to scale improvements beyond a single line, vendor, or site—and in Japan this is where OPC UA is becoming strategic.
In Japan, many sites must modernize under strict uptime constraints, with multi‑vendor assets spanning multiple generations. This makes incremental, standard‑based integration attractive compared with “big bang” replacement.
Why OPC UA fits the Japanese industrial reality
Japanese factories and plants are known for stability, kaizen, and long asset lifecycles. The practical challenge is heterogeneity by design: different machine generations, controllers, analyzers, and software stacks must coexist—sometimes for decades. Replacing everything at once is rarely realistic. OPC UA provides a secure, vendor‑neutral way to connect existing assets and new systems and modernize step by step.
Japan’s role in global supply chains reinforces the need for internationally aligned interfaces and shared data meaning. OPC UA’s governance and its ecosystem of Companion Specifications support that alignment without locking users into a single supplier’s format.
From connectivity to semantics: where adoption is heading
In Japan, the discussion is moving beyond “Can we connect?” to “Can we interpret data consistently?” Early projects often focused on basic connectivity—status, alarms, production counts, or energy. More recent deployments emphasize semantic consistency: quality, traceability, and repeatable integration.
A representative signal of this shift can be seen in the laboratory and analytical instruments domain. In Japan, the lab community has started promoting LADS OPC UA to enable plug‑and‑play interoperability across instrument platforms. A domestic proof‑of‑concept effort—driven by a leading Japanese chemical group together with an analytical‑instruments industry association—aims at easier and more secure monitoring, control, and logging, while reducing engineering time and vendor‑specific constraints. Here, “plug‑and‑play” means reduced integration effort under a shared information model—not “zero engineering.” (Based on public PoC announcements; names omitted.)
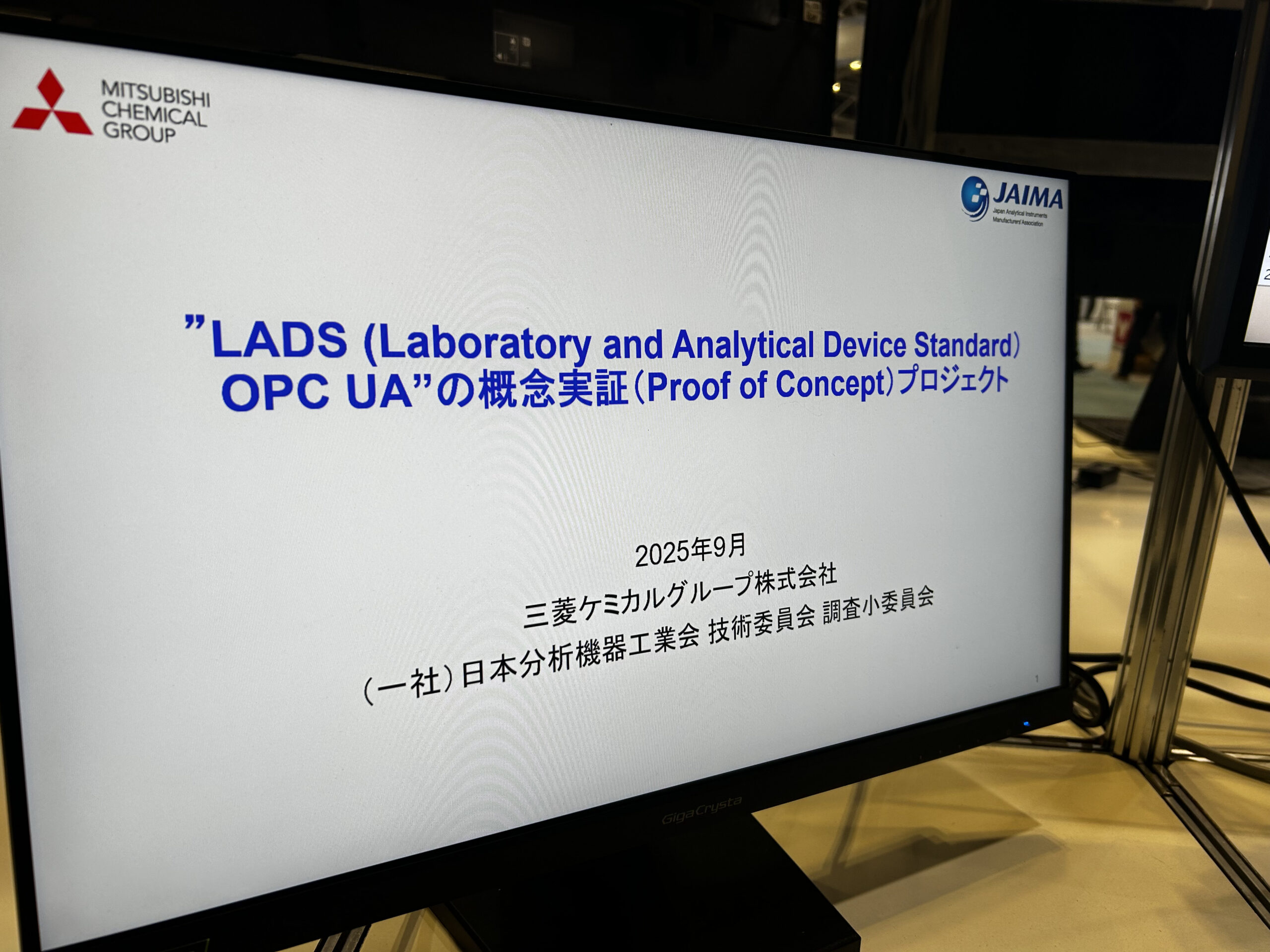 Figure 1. Public exhibition photo of a LADS OPC UA PoC in Japan; names visible are part of the booth display (no endorsement).
Figure 1. Public exhibition photo of a LADS OPC UA PoC in Japan; names visible are part of the booth display (no endorsement).
Brownfield reality: succeed by expanding in layers
Japan’s plants are “brownfield by default.” The question is how to modernize without disrupting production. A common pattern is to expand in layers: start with a narrow value case, standardize the interface at the system boundary, and then broaden scope once operations are stable.
A domestic case study published by a Japanese automation and control supplier illustrates this approach. A large refinery/petrochemical operator used the renewal timing of an aging Plant Information Management System (PIMS) to modernize data integration without a “big bang” replacement. The project reviewed connectivity between control systems, PIMS, and downstream applications and addressed cybersecurity concerns associated with legacy integration—such as the need, in some architectures, to open multiple firewall ports. By renewing the PIMS side to an OPC UA–compliant interface, the project improved security at the boundary while keeping operations practical. (Based on a public Japanese case study; names omitted.)
The renewal was designed for continuity. Alongside the PIMS update, the team standardized how multiple applications access PIMS data by consolidating related functions into a shared access component (for example, a common library). This reduced dependency on a specific PIMS package and made future replacement smoother—changing the shared component rather than refactoring each application individually. For brownfield environments, this “boundary first + decoupling” approach is a realistic way to keep modernization moving.
 Figure 2. Simulated plant environment used for OPC UA training and experimentation in Japan.
Figure 2. Simulated plant environment used for OPC UA training and experimentation in Japan.
Security is not a feature—it is an operating discipline
Japan’s industrial community has a high awareness of cybersecurity, especially in sectors linked to critical infrastructure. OPC UA’s security model (certificate‑based trust, encryption, and signing) is one reason it is considered industry‑grade. However, robust security is not achieved by specification alone. Real deployments require governance: certificate lifecycle management, trust boundaries, vendor access procedures, and exception handling for equipment that cannot be stopped.
Security success depends on people and process. A “secure default” is valuable, but sustainable operations require engineers who understand how to apply security profiles and maintain them over time.
The people challenge: making standard‑based skills accessible
A recurring barrier in Japan is not interest, but the shortage of engineers who can implement OPC UA correctly and confidently. Training exists, yet it is often vendor‑specific and focused on product usage rather than on architecture, information modeling, and security operations. Universities play an important role, but they cannot meet the demand for working professionals and mid‑career engineers across OT, IT, system integration, and cybersecurity.
Japan needs an accessible, standard‑focused learning foundation usable beyond academia: clear learning outcomes, hands‑on labs, and reference architectures that reflect real plant constraints. A shared “map” of skills also helps project teams align on competence—from foundational understanding to advanced implementation and security‑focused operation.
Looking forward
OPC UA is often described as a technology. In Japan, I would describe it as a commitment: to interoperability, long‑term maintainability, and secure operations. If we develop people as seriously as we develop specifications, OPC UA can become the backbone of trustworthy industrial digital transformation—inside Japan and across global value chains.
Toshiaki Honda, Ph.D.(Eng.) supports OPC UA education initiatives in Japan, including workshops and lectures for industrial cybersecurity audiences. His focus is practical adoption—information modeling, secure deployment, and long-term operability.